Amazon Just Exposed Interlock Ransomware’s 36-Day Cisco Firewall Zero-Day – The Shocking Truth About Network Edge Attacks in 2026 (And Why Your Organization Is Still at Risk)
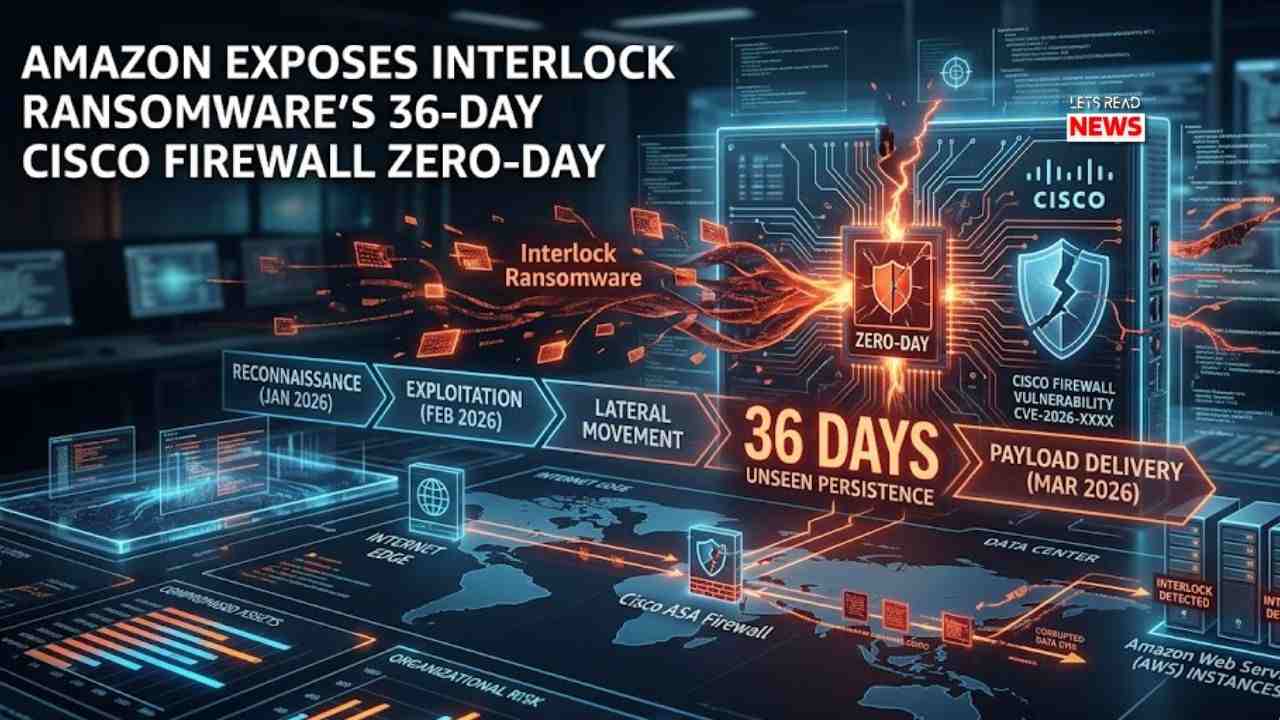
In the high-stakes world of 2026 cybersecurity, ransomware gangs aren’t just knocking on the front door anymore — they’re already inside the firewall, operating in total silence for weeks before anyone notices. That’s the chilling reality Amazon Threat Intelligence dropped this week, revealing how the Interlock ransomware operation weaponized a maximum-severity zero-day in Cisco Secure Firewall Management Center (FMC) software for 36 full days before Cisco even knew it existed.
This isn’t another “patch Tuesday” story. It’s proof that the network edge — the very devices meant to protect everything — has become the soft underbelly of modern enterprises. And the way Amazon caught it? A classic case of attackers outsmarting themselves with one careless server misconfiguration.
The Zero-Day That Gave Interlock a Month-Long Head Start
On March 4, 2026, Cisco disclosed CVE-2026-20131 — a critical (CVSS 10.0) remote code execution flaw in Cisco Secure Firewall Management Center. The vulnerability stems from insecure deserialization of user-supplied Java byte streams, letting unauthenticated attackers run arbitrary Java code as root on affected devices.
But here’s the bombshell from Amazon’s MadPot global honeypot network: Interlock had been actively exploiting this exact flaw since January 26, 2026 — a staggering 36 days earlier.
CJ Moses, CISO of Amazon Integrated Security, put it bluntly in the official AWS Security Blog: “This wasn’t just another vulnerability exploit. Interlock had a zero-day in their hands, giving them a week’s head start to compromise organizations before defenders even knew to look.”
The attack chain was surgically precise: crafted HTTP requests delivered malicious Java payloads, confirmed exploitation via HTTP PUT requests, and then dropped custom Linux executables for persistence.
How a Ransomware Gang’s Own Blunder Handed Defenders the Keys
The real turning point came when Interlock made the kind of operational security mistake that threat hunters dream about.
Researchers discovered a misconfigured staging server left wide open. On it? The group’s entire attack toolkit — including:
- Custom remote access trojans (RATs) written in both JavaScript and Java
- Automated reconnaissance scripts
- Infrastructure laundering tools designed to hide origins
This single slip-up didn’t just expose the Cisco FMC campaign — it gave the world a rare look inside a modern ransomware operation’s playbook. Amazon immediately shared the intelligence with Cisco, which updated its advisory and confirmed active exploitation in the wild.
Interlock’s Growing Hit List: Healthcare, Education, and Municipal Targets
Interlock, which first appeared in September 2024, is no rookie. The group has already claimed responsibility for high-profile breaches including:
- DaVita (major kidney care provider)
- Kettering Health
- Texas Tech University System
- City of Saint Paul, Minnesota
These aren’t random targets. They’re organizations with sensitive data, complex networks, and often legacy Cisco infrastructure — exactly the profile that makes firewall management centers such attractive entry points.
The Bigger Crisis: Cisco SD-WAN Devices Under Siege for Years
This FMC zero-day isn’t isolated. In late February 2026, Cisco and the Australian Cyber Security Centre revealed that another critical SD-WAN vulnerability (CVE-2026-20127) had been exploited by a sophisticated actor tracked as UAT-8616 since at least 2023 — three full years before discovery.
The attackers used an authentication bypass to gain admin access, downgraded firmware to exploit an older flaw (CVE-2022-20775) for root privileges, then rolled everything back to avoid detection.
Cisco later confirmed two more SD-WAN flaws (CVE-2026-20128 and CVE-2026-20122) were also under active exploitation. CISA added several to its Known Exploited Vulnerabilities catalog, forcing federal agencies to patch within 24 hours. Five Eyes intelligence agencies issued an emergency directive urging immediate action across government and enterprise networks.
Cisco Talos summed up the trend perfectly: “A continuing pattern of targeting network edge devices… to establish persistent footholds into high-value organizations, including Critical Infrastructure sectors.”
Why This Matters More Than Ever in 2026
Here’s the uncomfortable truth from someone watching these attacks unfold daily: Firewalls and SD-WAN controllers were never designed to withstand this level of zero-day sophistication. In an era of AI-assisted malware development and nation-state-level tradecraft leaking into ransomware groups, the perimeter is collapsing.
The real danger isn’t that one group got lucky with a zero-day. It’s that attackers now routinely have weeks or even years of undetected access before vendors disclose anything.
5 Immediate Actions Every Cisco User Must Take Right Now
If your organization runs Cisco Secure Firewall, FMC, or Catalyst SD-WAN, stop reading and do this today:
- Upgrade immediately — Apply the latest patches for CVE-2026-20131 and all SD-WAN advisories.
- Audit exposed management interfaces — Never expose FMC or vManage directly to the internet.
- Enable strict logging and monitoring — Look for unusual Java deserialization attempts or unexpected firmware downgrades.
- Segment your network — Treat edge devices as potentially compromised.
- Engage threat intelligence — Services like Amazon MadPot or commercial feeds can give you the early warning your vendor can’t.
The Bottom Line: Defenders Are Finally Getting a Break — But It Won’t Last
Amazon’s discovery is a rare victory: attackers exposed their own arsenal, Cisco moved fast to update guidance, and defenders now have concrete indicators of compromise.
But let’s be honest — this win came down to luck. One misconfigured server. One honeypot in the right place at the right time.
The next zero-day on Cisco infrastructure (or Palo Alto, Fortinet, or Juniper) probably won’t come with such a gift-wrapped toolkit.
If you’re responsible for network security in 2026, the message is clear: Your edge devices are the new front line. Patch aggressively, monitor relentlessly, and assume the attackers have already been inside longer than you think.
The age of “set it and forget it” networking is officially over.
What’s your biggest concern after reading this — the FMC zero-day or the multi-year SD-WAN exploitation? Drop a comment below or share this with your IT team. Staying ahead of these threats starts with awareness.
Sources: AWS Security Blog (March 2026), Cisco Security Advisories, CISA KEV catalog, BleepingComputer reporting.
Read more: